Web UI renders javascript code in ML Engine name leading to XSS
September 12, 2024

Products Impacted
The vulnerability is present in all versions of the MindsDB project.
CVSS Score: 9.0
AV:N/AC:L/PR:L/UI:R/S:C/C:H/I:H/A:H
CWE Categorization
CWE-79: Improper Neutralization of Input During Web Page Generation (‘Cross-site Scripting’)
Details
To exploit this vulnerability, an attacker authenticated to a MindsDB instance could craft a dataset as shown below:
feature1,quality
<img src='#' onerror=alert("sample1") />, 5Once this has been created, the attacker can upload the file, and the javascript code will be run in the victim’s browser when they attempt to view the contents of the dataset within the UI, as shown below:
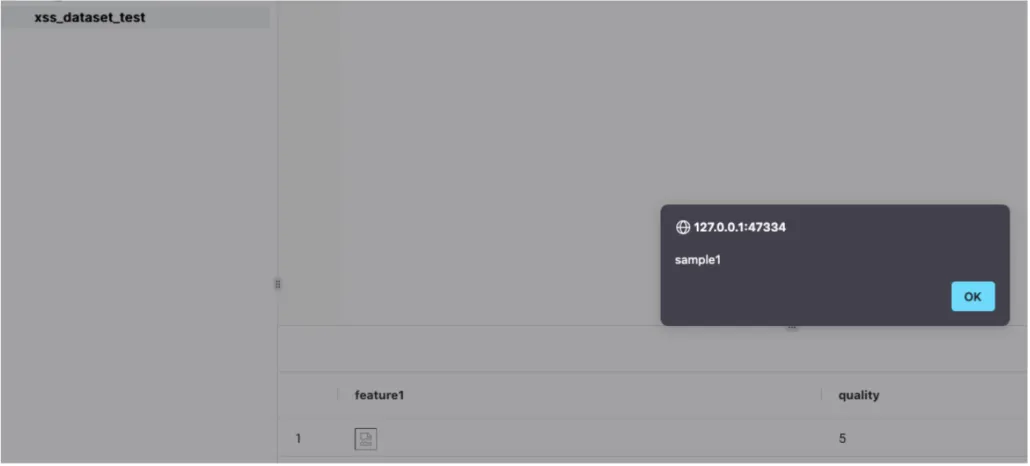
As can be seen in the above screenshot, the rendering occurs within the table.
Timeline
July, 12 2024 — Vendor disclosure via process outlined in SECURITY.md
July, 23 2024 — Update made to project Github repository in version v24.7.4.1 replacing use of ‘eval’ with ‘ast.literal_eval’. This affects some of our submitted CVEs and can be seen here
July, 29 2024 — Follow up email sent to vendor
September, 6 2024 — Final attempt to reach out to vendor prior to public disclosure date
September, 10 2024 — Received response from vendor saying they had put a number of changes in place to “mitigate some or all of the reported issues”
September, 12 2024 — Public disclosure
Project URL
https://github.com/mindsdb/mindsdb
Researcher: Kieran Evans, Principal Security Researcher, HiddenLayer
Researcher: Leo Ring, Security Research Intern, HiddenLayer
Researcher: Kasimir Schulz, Principal Security Researcher, HiddenLayer
Related SAI Security Advisory
February 26, 2026
Flair Vulnerability Report
An arbitrary code execution vulnerability exists in the LanguageModel class due to unsafe deserialization in the load_language_model method. Specifically, the method invokes torch.load() with the weights_only parameter set to False, which causes PyTorch to rely on Python’s pickle module for object deserialization.
November 26, 2025
Allowlist Bypass in Run Terminal Tool Allows Arbitrary Code Execution During Autorun Mode
When in autorun mode, Cursor checks commands sent to run in the terminal to see if a command has been specifically allowed. The function that checks the command has a bypass to its logic allowing an attacker to craft a command that will execute non-allowed commands.