Improper access control arbitrary allows account creation
June 9, 2025

Products Impacted
This vulnerability is present in all versions of BackendAI. We tested on version 25.3.3 (commit f7f8fe33ea0230090f1d0e5a936ef8edd8cf9959).
CVSS Score: 9.8
CVSS:3.0/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
CWE Categorization
CWE-284: Improper Access Control
Details
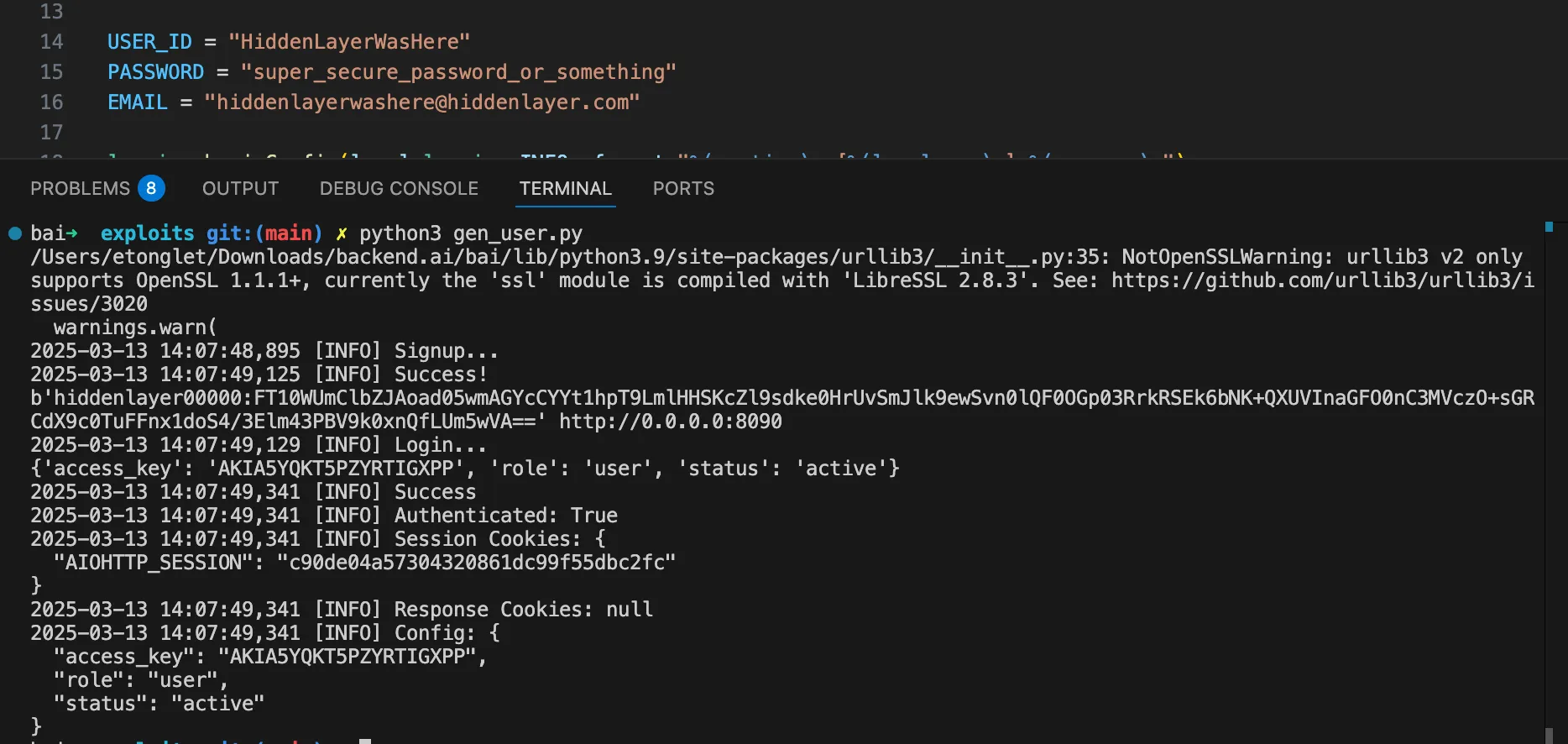
To sign up, an attacker can use the API endpoint /func/auth/signup. Then, using the login credentials, the attacker can access the account.
To reproduce this, we made a Python script to reach the endpoint and signup. Using those login credentials on the endpoint /server/login we get a valid session. When running the exploit, we get a valid AIOHTTP_SESSION cookie, or we can reuse the credentials to log in.
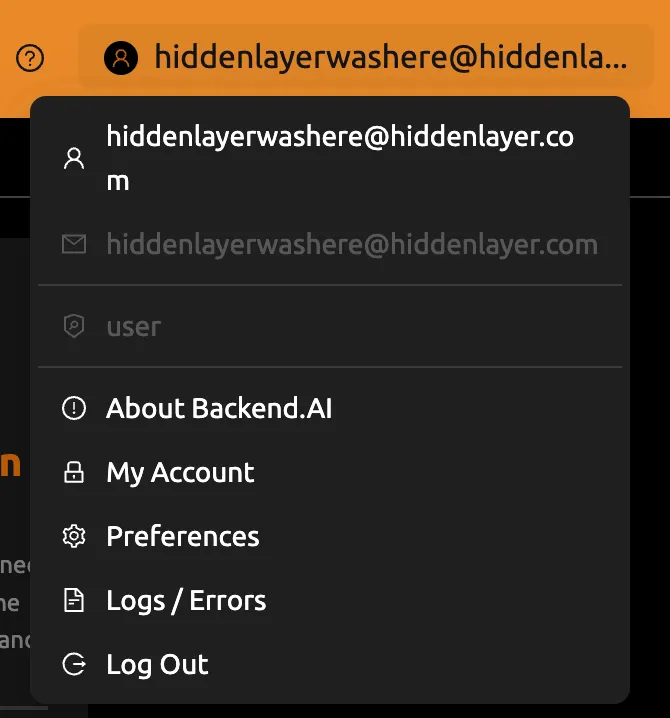
We can then try to login with those credentials and notice that we successfully logged in
Related SAI Security Advisory
February 26, 2026
Flair Vulnerability Report
An arbitrary code execution vulnerability exists in the LanguageModel class due to unsafe deserialization in the load_language_model method. Specifically, the method invokes torch.load() with the weights_only parameter set to False, which causes PyTorch to rely on Python’s pickle module for object deserialization.
November 26, 2025
Allowlist Bypass in Run Terminal Tool Allows Arbitrary Code Execution During Autorun Mode
When in autorun mode, Cursor checks commands sent to run in the terminal to see if a command has been specifically allowed. The function that checks the command has a bypass to its logic allowing an attacker to craft a command that will execute non-allowed commands.